-
What Is Business Email Compromise (BEC)?
- Business Email Compromise Explained
- Mechanics Behind Business Email Compromise
- BEC as a Strategic Component in Multistage Attacks
- Use Cases: BEC Campaigns with Measurable Impact
- Detecting BEC in Enterprise Environments
- Practical Defenses Against BEC at the Identity Layer
- Why BEC Is a Board-Level Concern
- Business Email Compromise FAQs
- What Are Business Email Compromise (BEC) Tools and Technologies?
What Are Types of Business Email Compromise (BEC) Scams?
Business email compromise (BEC) scams are sophisticated fraud schemes that target companies by exploiting email communications to request payments. These scams can have devastating financial consequences for businesses.
The most common types of BEC scams include:
- CEO Fraud, where attackers pose as company executives to request urgent wire transfers
- Invoice Manipulation, involving fake or altered invoices to redirect payments
- Phishing, where scammers use deceptive emails to gain access to sensitive information
Understanding these scams is crucial for businesses to implement effective preventative measures and maintain secure communication channels.
Key Characteristics of BEC Scams
A business email compromise (BEC) scam is a type of cyber fraud that typically involves manipulating business email accounts to trick companies, their employees, or their partners into transferring funds or sensitive information to the scammers.
BEC scams are known for their sophistication and often involve social engineering techniques. Key characteristics of BEC scams include:
- Impersonation: Scammers often impersonate high-level executives, employees, or business partners. They might use email addresses similar to legitimate ones, sometimes differing by just one letter or symbol.
- Urgent Requests: The fraudulent emails usually contain requests for urgent wire transfers or prompt action, creating a sense of urgency and reducing the likelihood of the recipient verifying the request.
- Manipulated Instructions: In invoice scams, the fraudsters might request changes to bank account details for invoice payments, transferring funds to the scammer's account instead of the intended recipient.
- Confidential Requests: Scammers might ask the recipients to keep the request confidential, further preventing verification with other team members or superiors.
- Data Theft: Some BEC scams focus on obtaining confidential data, like employee tax information, rather than directly stealing money.
These scams can be highly damaging financially and reputationally to businesses. Therefore, awareness and training, along with strong internal protocols for verifying and processing requests for money transfers or sensitive information, are crucial in combating BEC scams.
Most Common Types of BEC Scams
With more people working in remote and hybrid environments, BEC scams are more prevalent and pernicious. Fraudsters are always looking to take advantage of any perceived weakness. When workers are more isolated, scammers believe they are susceptible to phishing, spoofing, or social engineering.
Advances have also abetted scammers in social engineering, automation, artificial intelligence, and machine learning. These tools make BEC scams more sophisticated, stealthy, and predatory. Scams often involve careful planning and may include prior surveys to make the fraudulent requests seem more legitimate.
While BEC scams have been around for years, they are more dangerous than ever because today’s cybercriminals are better funded and access better tools. Even when cybersecurity teams know the types of scams used by adversaries and their most common techniques, organizations must be constantly vigilant to prevent and respond quickly and comprehensively to attacks.
The most common types of BEC scams are:
- Executive or CEO Fraud: Scammers impersonate a company's high-ranking executive, typically the CEO, and send an email to employees, usually in the finance department. This involves tricking employees into transferring funds or revealing sensitive information. The fraudsters often send urgent requests for wire transfers or confidential data.
- Lawyer (or Attorney) Impersonation: Attackers pose as lawyers or legal representatives, usually under the guise of confidentiality and urgency. They may request immediate action regarding financial transactions or sensitive information.
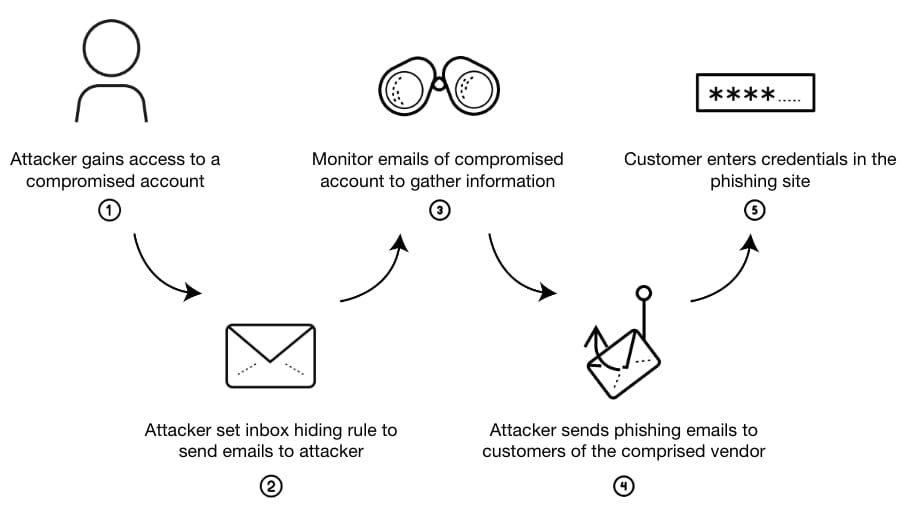
- Account Compromise/Account Takeover: An attacker gains unauthorized access to an employee's email account through phishing or malware to request invoice payments from vendors listed in their email contacts. Once in, they send fraudulent requests or modify payment details in legitimate transactions. The scammer collects payments sent to these fraudulent bank accounts.
- Credential Theft: This involves stealing login credentials, such as usernames and passwords, often through phishing attacks. With these credentials, attackers access sensitive systems and data, initiating fraudulent transactions.
- Data Theft: Fraudsters target human resources or accounting departments to extract personally identifiable information or tax statements of employees and executives. Attackers aim to steal valuable information by targeting employees with access to sensitive data. This data can be used for malicious purposes, including identity theft and further BEC scams.
- False Invoice Scheme: An invoice appears to be from a legitimate supplier but is actually from a fraudster. Companies with international suppliers are often targeted since they are less likely to verify invoices in person.
Methods Used in BEC Scams
Cybercriminals now use automation, AI, and machine learning to launch more frequent and targeted BEC attacks. They focus on vulnerable individuals or departments. Cybersecurity professionals must understand who and how they may be targeted. This knowledge helps them decide where to invest in preventative tools and technologies, like Zero Trust. It also guides decisions about how to conduct employee training and develop a cyber-aware culture.
BEC scams use various tactics, including:
- Domain impersonation
- Gaining access to email accounts
- Phishing attacks
- Credential stuffing
- Social engineering
- Spear phishing
- Manipulation of email threads
Scammers create fake email addresses and domains similar to legitimate ones to trick recipients. They can gain access to email accounts through phishing attacks, and once inside, they can send fraudulent requests or intercept legitimate transactions.
Phishing emails appear legitimate and often replicate the branding and tone of real companies. Scammers also manipulate human psychology to trick individuals into breaking normal security procedures. Spear phishing targets specific individuals or companies, while thread hijacking involves fraudsters posing as one of the parties to redirect a transaction or request confidential information.
BEC scams, which employ a mix of technical deception and psychological manipulation, represent a significant threat to organizations. Awareness and education on these methods are essential to a comprehensive strategy to combat these sophisticated fraud schemes.
Real-World Examples of the Largest BEC Scams
Business email compromise (BEC) scams have led to significant financial losses globally. Some of the largest and most impactful BEC scams, often reported by the FBI and other law enforcement agencies, include:
- Evaldas Rimasauskas Scam: Evaldas Rimasauskas, a Lithuanian national, orchestrated a scam amounting to over $100 million by targeting two major U.S. technology companies, identified by media reports as Google and Facebook. He sent phishing emails impersonating a legitimate Asian manufacturer, leading these companies to transfer large sums of money into bank accounts he controlled.
- In 2015, a major manufacturer of wireless data communication and wireless broadband products reported approximately $46.7 million in losses due to a BEC scam. Scammers targeted employees and initiated unauthorized international wire transfers.
- An Austrian aerospace manufacturer lost about €50 million (approximately $54 million) in 2016 due to a BEC scam. An employee transferred the amount to a fraudulent account following an email request that appeared to come from the CEO.
- In 2019, a car parts manufacturer was defrauded of about 4 billion yen (approximately $37 million). The company transferred the funds to a fraudulent account after receiving deceptive payment requests in a BEC scam.
- In 2015, an agricultural product trading firm lost $17.2 million due to a BEC scam. An executive was tricked into wiring the funds to a bank in China, following instructions from emails that appeared to be from the company's CEO and a legal advisor.
These examples demonstrate the scale and sophistication of BEC scams, emphasizing the importance of robust security measures and employee education in detecting and preventing such fraudulent activities.
Prevention Strategies for BEC Scams
To effectively combat business email compromise (BEC) scams, organizations must implement a multi-layered approach that includes both technical solutions and human-centric strategies. Here are some key prevention strategies:
Implementing Strong Internal Control Processes
Establishing robust internal controls is fundamental in preventing BEC scams. This involves creating clear protocols for financial transactions, such as dual-approval processes for wire transfers and changes to vendor payment details. Regular audits and reviews of financial procedures can also help identify and rectify any vulnerabilities.
Using Email Authentication Protocols
Deploying email authentication measures like DMARC (Domain-based Message Authentication, Reporting, and Conformance), SPF (Sender Policy Framework), and DKIM (DomainKeys Identified Mail) can significantly reduce the risk of email spoofing. These protocols help verify that the emails are from the stated source, thus preventing domain impersonation.
Deploying Advanced Email Security Tools
Investing in advanced email security solutions that include phishing detection, anomaly detection, and advanced threat protection can provide an additional layer of defense. These tools can identify suspicious email patterns, malicious links, and attachments, reducing the likelihood of successful BEC attacks.
Employee Training and Awareness Programs
Human error often plays a significant role in the success of BEC scams. Regular training sessions to educate employees about the latest scamming techniques, recognize phishing emails, and follow internal protocols are crucial. Simulated phishing exercises can also be an effective way to assess and improve workforce preparedness.
Verification Procedures
Implement a policy verifying any unexpected or unusual requests, especially those involving financial transactions or sensitive information. This can include calling the requester using a known phone number (not the one provided in the suspicious email) to confirm the request's legitimacy.
Limiting Access to Sensitive Information
Restricting access to sensitive information and implementing a 'need to know' policy can minimize the impact if an email account is compromised. This also includes regularly updating and managing access privileges as organizational roles change.
Regular Software Updates and Patch Management
Ensuring that all systems, including email clients and security software, are regularly updated with the latest patches can close security vulnerabilities that attackers might exploit.
Creating a Response Plan
It is vital to have a well-defined incident response plan in case of a suspected BEC attack. This plan should include steps for isolating the incident, assessing the damage, and reporting the scam to relevant authorities.
Organizations can significantly enhance their defenses against BEC scams by incorporating these strategies. It's important to remember that as scam tactics evolve, so should the prevention methods, requiring ongoing vigilance and adaptation.