Introduction
Threat actors often leverage scheduled tasks to execute malicious payloads persistently across endpoints. When a scheduled task is created remotely in an uncommon manner, it may indicate a persistence method or execution of unauthorized commands.
The "Endpoint Initiated Uncommon Remote Scheduled Task Creation" playbook in Cortex XSIAM’s Response and Remediation Pack provides an automated approach to detecting, investigating, and remediating such threats. By leveraging advanced analytics and integrations within Cortex XSIAM®, this playbook helps security teams efficiently neutralize suspicious scheduled task creations before they escalate into major incidents.
Threat Overview
Attackers frequently use remote scheduled tasks for:
- Executing malicious scripts on remote hosts to establish persistence.
- Deploying backdoors or launching malware across multiple endpoints.
- Running scheduled commands to evade detection and automate attacks.
This playbook is triggered when an "Uncommon Remote Scheduled Task Creation" alert is generated on the source host that initiated the remote task. It then proceeds with analysis, investigation, and remediation to determine the legitimacy of the activity.
Purpose of the Playbook
The "Endpoint Initiated Uncommon Remote Scheduled Task Creation" playbook is designed to automate containment and response actions by following a structured investigation process.
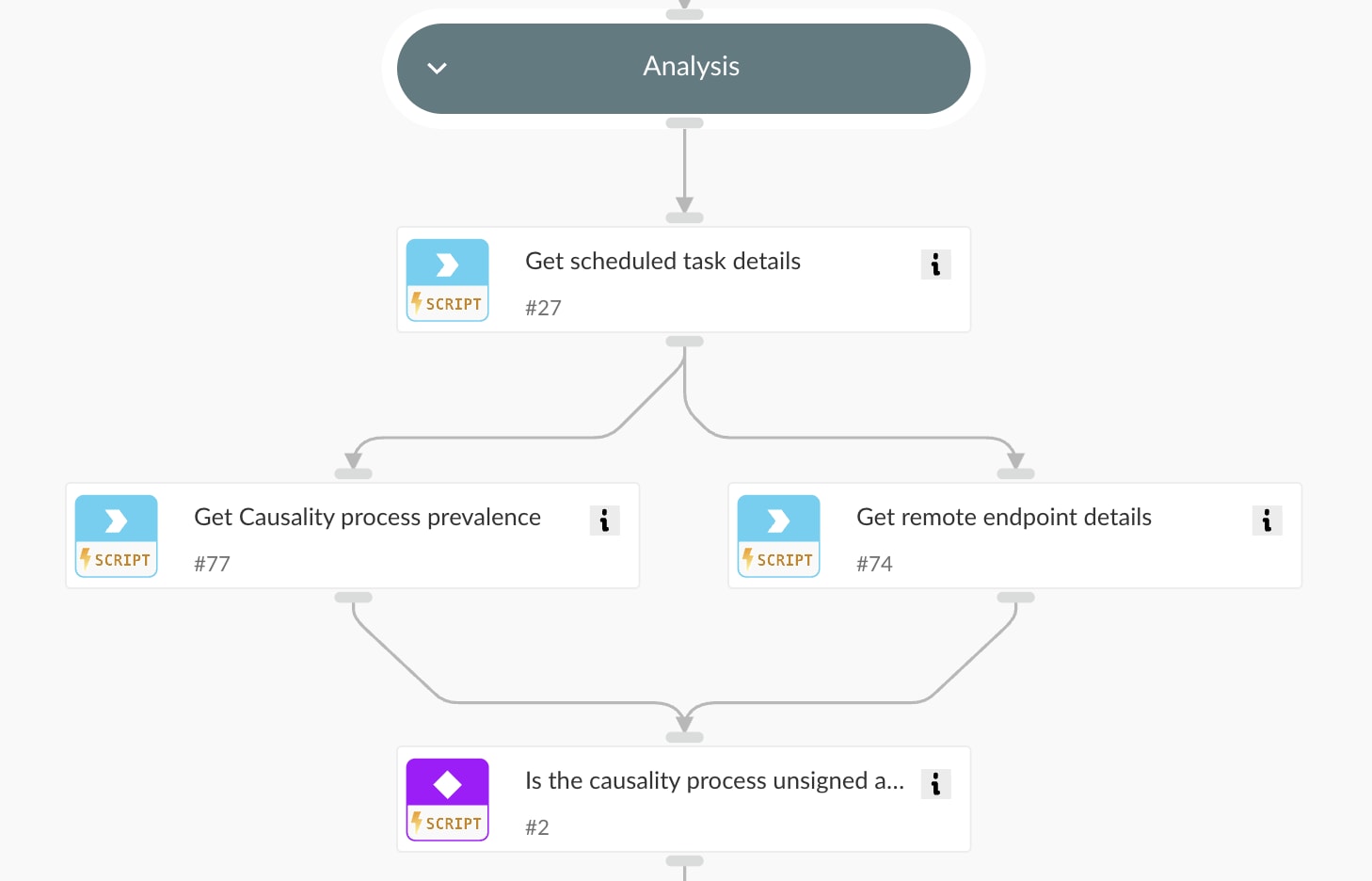
1. Analysis
- Verifies whether the causality process (the originating process of the scheduled task) is signed and prevalent.
- If the process is unsigned and uncommon, it is flagged for immediate remediation.
2. Investigation
The playbook performs a multi-layered investigation, including:
- Searching for related XSIAM alerts on the endpoint for MITRE ATT&CK® techniques such as:
- T1202 - Indirect Command Execution
- T1021 - Remote Services
- Investigating alerts on the remote endpoint to identify potential attack patterns.
- Analyzing the command-line parameters for indicators of malicious activity.
![Fig 2: Segment of playbook illustrating automated multi-layered investigation]()
Fig 2: Segment of playbook illustrating automated multi-layered investigation
3. Remediation
If malicious intent is confirmed, the playbook automatically:
- Disables the scheduled task on the remote host.
- Terminates the causality process responsible for creating the task.
- Closes the alert after ensuring all mitigation steps have been executed.
This comprehensive approach ensures that malicious scheduled tasks are promptly neutralized, preventing further compromise.

Security Challenges & How This Playbook Solves Them
1. Identifying Suspicious Remote Scheduled Tasks
Due to the volume of legitimate system activity, manually detecting malicious scheduled task creation is challenging. This playbook automates anomaly detection by correlating behavior with MITRE ATT&CK techniques and in-depth command analysis.
2. Validating Process Legitimacy
Not all scheduled tasks are malicious. The playbook evaluates the signing status and prevalence of the process to distinguish benign administrative tasks from potential threats.
3. Blocking Malicious Tasks Before Execution
By automatically disabling malicious scheduled tasks, the playbook prevents adversaries from leveraging remote execution techniques.
4. Rapid Incident Response
Automating remediation ensures security teams can respond in real time, reducing dwell time and potential impact.
Conclusion
The "Endpoint Initiated Uncommon Remote Scheduled Task Creation" playbook in Cortex XSIAM strengthens endpoint security by automating threat detection and response. By leveraging process analytics, command-line forensics, and automated remediation, this playbook ensures that suspicious scheduled tasks are swiftly neutralized.
To deploy this playbook and enhance your autonomous SOC capabilities, visit the Cortex XSIAM Response and Remediation Pack.
